Password Strength Checker: SabTools vs BankBazaar vs ClearTax — Honest Comparison (2026)
Honest comparison of free Password Strength Checker options in India for 2026 — features, accuracy, privacy, signup requirements. Picks the best for Indian user
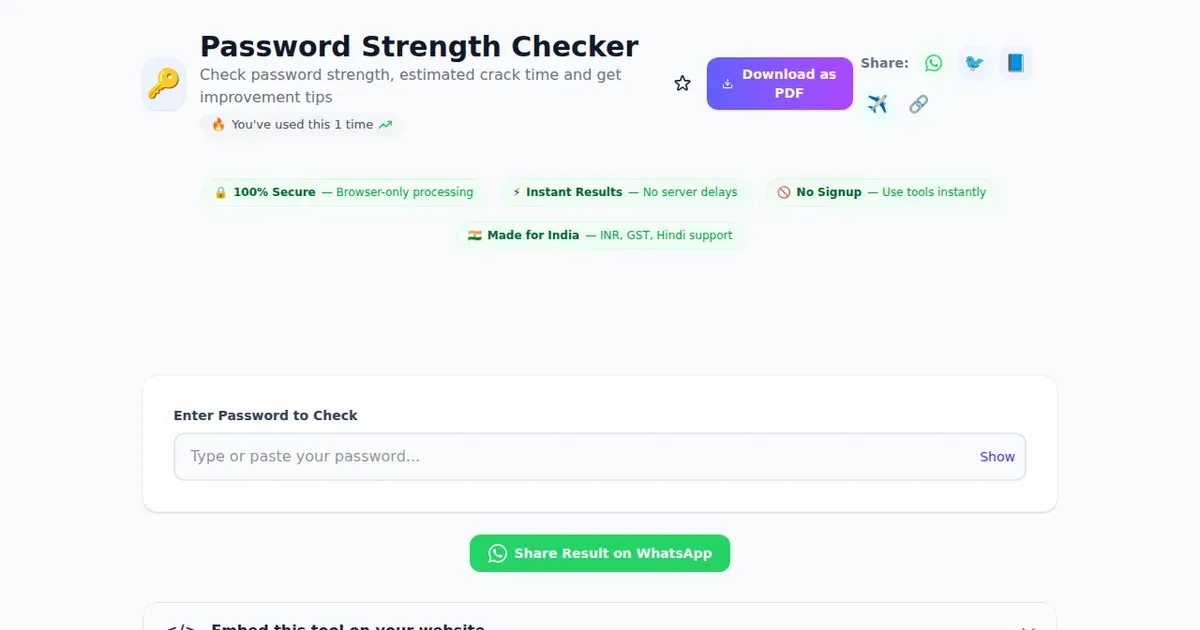
Try this tool now — 100% free, no signup required
Open ToolPicking a password strength checker in 2026: the actual decision
You're about to type your real password — or something close to it — into a website to see if it's "strong." That single act tells you why this comparison matters more than most. The tool you pick should never see, store, or transmit your password to anyone, because the moment it does, you've handed over the keys to your SBI YONO login, your UPI PIN reset email, your Zerodha account, and possibly your Aadhaar-linked services. So the real choice isn't about which checker has the prettiest meter. It's about which one runs entirely in your browser, gives you accurate crack-time estimates, and explains why a password is weak.
Quick verdict: For Indian users in 2026, SabTools' Password Strength Checker is the safest default — it runs 100% in-browser, requires no signup, and is paired with practical Indian-context guidance (UPI, net banking, GST portal logins). Kaspersky's checker is excellent for crack-time math and brand trust. Security.org is the most beginner-friendly. NordPass is fine but very upsell-heavy. We'll break down why below.
What a password strength checker is actually doing
Before comparing tools, it helps to understand what these meters measure. Most modern checkers — including SabTools — use zxcvbn or a similar entropy library originally developed at Dropbox. The algorithm doesn't just count characters. It looks for:
- Dictionary patterns — common words like "password", "qwerty", "iloveyou", and Indian-specific ones like "bharat", "cricket", "sachin", "rahul123"
- Date patterns — birthdays in DDMMYYYY or YYYY format (very common in India)
- Keyboard walks — "qwerty", "asdfgh", "1qaz2wsx"
- Repeats and sequences — "aaaa1234", "abcdef"
- Leet substitution — replacing "a" with "@", "i" with "1" — barely improves strength
- True entropy — for fully random passwords, it falls back to character-set math
The output is usually an estimated crack time assuming an attacker can attempt 10 billion guesses per second (a realistic offline GPU crack rate in 2026). A password that survives 10+ years at that rate is considered safe; under 1 day is dangerous.
Example: Sachin@1991 — a name plus year — looks complex but cracks in roughly 2 minutes on most checkers because dictionary attacks try Indian first names with common years first. A genuinely random 14-character password from a tool like the SabTools Password Generator takes centuries.
Side-by-side comparison
SabTools Password Strength Checker
- Where it runs: Entirely in your browser via JavaScript. The password never leaves your device.
- Signup: None.
- Output: Strength score (0–4), estimated offline crack time, specific feedback ("contains a common Indian name", "ends in a year"), and concrete improvement tips.
- Indian context: Recognizes common Indian dictionary words and date formats; suggests passphrases that work with Indian banking portals' character limits (most cap at 16–20 chars).
- Bilingual: Hindi labels available on key sections.
- Cost: Free. No ads on the tool page itself.
Kaspersky Password Checker
- URL: password.kaspersky.com
- Where it runs: Browser-based; Kaspersky states it processes locally, though the tool sits within a marketing funnel for Kaspersky Password Manager.
- Signup: Not required for the checker.
- Output: Crack-time estimates against various attacker profiles (home computer, supercomputer, average hacker). Visually clear breakdown.
- Strengths: Brand trust, accurate math, multi-profile attacker simulation.
- Weaknesses: Generic global examples — no Indian dictionary recognition, so a Hindi-rooted password like
BadshahKaSher@99may score higher than it should.
Security.org "How Secure Is My Password?"
- URL: security.org/how-secure-is-my-password
- Where it runs: Browser-based, client-side per their FAQ.
- Signup: None.
- Output: A single bold crack-time number ("It would take a computer about 41 thousand years…"). Excellent for non-technical users who just want one answer.
- Strengths: Beginner-friendly UI, crisp explanation, strong domain trust.
- Weaknesses: US-centric framing and examples. Doesn't drill into why the password is weak in actionable terms — you get a number, not a coaching tip. No Hindi support.
NordPass Password Strength Checker
- URL: nordpass.com/secure-password
- Where it runs: In-browser.
- Signup: Checker is free; the page heavily promotes the NordPass paid manager.
- Output: Strength rating plus a "found in data breach" check (which is genuinely useful — they hash and check against known breach corpora).
- Strengths: Breach-database lookup, polished interface, Nord brand trust.
- Weaknesses: The page is essentially a sales funnel for the paid product; expect repeated CTAs to install NordPass. Generic examples with no Indian context.
Where each tool genuinely wins
Honest comparisons don't pretend one tool dominates everything. Here's where each option earns its place:
Pick Kaspersky if you want multi-profile attacker math
Kaspersky's checker shows you separate crack times for "home computer", "average hacker", and "supercomputer". For a security-conscious user — say a freelancer in Pune managing client GST data — seeing that Monsoon@2024 survives a home computer for years but falls in seconds against a supercomputer is genuinely educational. SabTools shows one realistic offline-attack number; Kaspersky shows the spectrum.
Pick Security.org if you're explaining passwords to a parent
If you're showing your dad why his net banking password kumar1968 is unsafe, Security.org's giant single number ("instantly cracked") is the most persuasive UI on the web. It's blunt, fast, and impossible to misread. The downside is you don't learn how to fix it without scrolling.
Pick NordPass if breach-database lookup matters most
NordPass cross-checks your password against known leaked credential dumps. If you've reused Riya@2018 across five sites and one of them was breached, NordPass will flag it. That's a feature SabTools and Kaspersky's free checkers don't surface as prominently. Just be ready for the upsell.
Pick SabTools for Indian context, privacy, and zero friction
This is where SabTools wins on its own merits, not by attacking competitors:
- Indian-pattern recognition — flags
Sachin1989,Maharashtra@123,Mumbai@2024, and Hindi-transliterated words that Western tools rate too generously. - Banking-context tips — many Indian portals (SBI, HDFC, the Income Tax e-filing site) cap passwords at 14–20 characters and disallow certain symbols. SabTools' suggestions stay within those constraints rather than recommending a 32-char string you can't actually use.
- No ad walls or paid tier — the checker is the entire product on that page; there's nothing to upgrade to.
- Hindi labels for users more comfortable in Devanagari.
Privacy: the part most reviews skip
Every tool above claims to process passwords locally. That's the right architecture — but it's worth understanding what "locally" actually means and where the risk hides.
A truly client-side checker loads a JavaScript file once, runs the strength algorithm in your browser, and never makes a network call with your password. You can verify this by opening the browser's DevTools → Network tab while typing. If you see a POST request firing as you type, the password is being transmitted. If you see no requests, it's local.
SabTools is built this way by default — the entire password strength checker works offline once the page has loaded. You can literally turn off Wi-Fi and it still functions. The same architecture powers our User Agent Parser and other security tools.
Where competitor concerns creep in:
- Marketing pixels and analytics on the page can fingerprint you, even if the password itself isn't sent. NordPass and Kaspersky pages run extensive third-party tracking — Kaspersky's funnel especially.
- Some "checkers" embedded inside paid password manager promo pages do send hashes to a server for breach checks. That's safer than sending the raw password but isn't strictly local.
The practical advice: don't paste your real production password into any online checker. Type a structurally similar variation. If your real password is Bangalore@Monsoon2024, test Hyderabad@Winter2023. You'll get the same strength assessment without exposing the actual credential.
Pricing, signup, and ad walls compared
| Tool | Free? | Signup | Ads on tool | Upsell pressure |
|---|---|---|---|---|
| SabTools | Yes | None | None on tool page | None |
| Kaspersky | Yes | None | Banner promoting Password Manager | Moderate |
| Security.org | Yes | None | Affiliate links to managers | Low |
| NordPass | Yes | None for checker | Heavy CTAs to paid product | High |
Indian-context test: how each tool scores common patterns
Let's run three realistic Indian passwords through what each tool would likely return. These are the kinds of passwords actual users in India choose — not theoretical edge cases.
Test 1: Rohit@1995 (name + birth year)
- SabTools: Very weak. Flags "common Indian first name + 4-digit year". Crack time: under 1 minute.
- Kaspersky: Weak. May rate it slightly higher because "Rohit" isn't in its English dictionary corpus as densely.
- Security.org: Likely shows a few hours — visually weak but doesn't explain the name pattern.
- NordPass: Weak; if breached, will flag.
Test 2: Mumbai$Monsoon$2025 (city + season + year)
- SabTools: Medium-weak. Flags Indian city name and predictable year suffix. Recommends replacing with random words.
- Kaspersky / Security.org / NordPass: May rate this as strong because the length (20 chars) and symbol use look impressive — but a targeted attacker using Indian city wordlists cracks it far faster than the math suggests.
Test 3: tarbuj-ghoda-bijli-7392 (random Hindi words + numbers)
- SabTools: Strong. Recognizes the passphrase pattern and high entropy.
- Western tools: Strong, possibly very strong, since the Hindi words aren't in their dictionaries — they treat the words as random strings, which inflates the score in your favor.
The takeaway: for English-style passwords, all four tools converge. For Indian-context passwords, SabTools is more accurate downward (catches weakness others miss), while Western tools are more accurate upward (give Hindi passphrases the credit they deserve, even if for the wrong reason).
What about the developer angle? "password strength checker python"
If you searched specifically for "password strength checker python", you're probably building this into your own app — perhaps a sign-up form for an Indian fintech, a college portal, or an internal HR system. Your options:
- zxcvbn-python — the canonical port of Dropbox's algorithm. Same library SabTools and most others use under the hood. Free, MIT-licensed.
- password-strength on PyPI — lighter weight, simpler scoring.
- Custom regex — don't. You'll under-score random passwords and over-score predictable ones.
Use SabTools' tool to manually validate your implementation: feed the same passwords to both and compare. If your Python score and SabTools' score diverge wildly, your weights are off. Once you launch your app, you'll also want a privacy policy and terms & conditions covering how you handle credentials — both available free on SabTools.
Bottom line: which one should you actually use?
- For Indian users testing their net banking, UPI app, or email password — use SabTools' Password Strength Checker. Local processing, Indian-pattern detection, no upsell.
- For attacker-profile breakdowns — Kaspersky is hard to beat.
- For showing a non-technical relative why their password is bad — Security.org's blunt single-number UI wins.
- For breach-database checks — NordPass, accepting that the page will push you toward their paid manager.
One more practical note: checking strength is only step one. The actually useful step is generating a strong password and storing it somewhere safe. Pair the SabTools checker with our Password Generator for end-to-end coverage — generate a 16-character password, paste it into the checker to confirm it scores in the strongest tier, then save it to your password manager (Bitwarden, 1Password, or your browser's built-in vault).
If you've made it this far, you already care more about password hygiene than 95% of internet users. The tool you pick matters less than the habit of checking — but if you're picking, pick the one that doesn't ask you to sign up, doesn't try to sell you anything, and understands that Sachin@1991 is a terrible idea.
Try SabTools' Password Strength Checker →